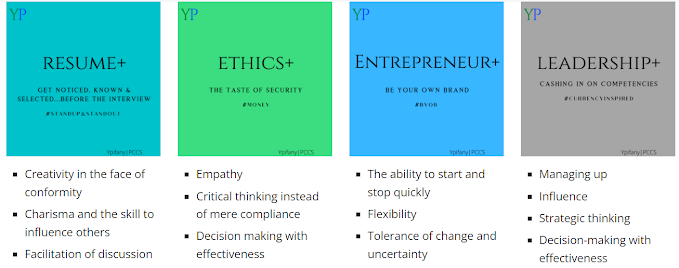
Current courses I'm working on
“Understanding by Design is a book written by Grant Wiggins and Jay McTighe that offers a framework for designing courses and content units called “Backward Design.” Instructors typically approach course design in a “forward design” manner, meaning they consider the learning activities (how to teach the content), develop assessments around their learning activities, then attempt to draw connections to the learning goals of the course. In contrast, the backward design approach has instructors consider the learning goals of the course first. These learning goals embody the knowledge and skills instructors want their students to have learned when they leave the course. Once the learning goals have been established, the second stage involves consideration of assessment. The backward design framework suggests that instructors should consider these overarching learning goals and how students will be assessed prior to consideration of how to teach the content. For this reason, backward design is considered a much more intentional approach to course design than traditional methods of design.”-- https://cft.vanderbilt.edu/guides-sub-pages/understanding-by-design/
Below is an example of how I used
backward design to plan a cybersecurity learning activity for a cybersecurity nonprofit organization.
Stage
1—Environmental Scan (Rich Picture)/To illustrate the main elements &
relationships to be considered in creating the situation we desire.
“We are
interested in a situation that: (1) produces skilled, diverse cybersecurity
candidates, (2) diversifies the cybersecurity talent pipeline and (3) narrows
the cybersecurity skills gap.”
·
Enhanced
digital citizens
·
We
are collaborators
·
Learners
have a choice to self-imposed constraints
Stage 1—Stakeholders
|
Stakeholder Role |
Influence and/or have an impact on |
Stake (material and non-material
interests) |
|
|
Chief Information Security Officer |
Cyber-L design and outcomes; organization’s decision-making
environment |
Skilled candidates |
|
|
Cyber-L Participant |
Cyber-L design and outcomes; learning artifacts; marketing |
Diverse candidates |
|
|
Chief Risk Officer |
Cyber-L design |
Diversified talent pipeline |
|
|
Cyber team (staff) |
Learning transfer environment;
|
Narrowed skills gap |
|
|
Organizational Leaders (CEO) |
Choice of development programs; organization’s decision-making
environment; absorptive capacity |
Business continuity; Organization’s reputation; Access to quality information for
decision-making |
|
|
|
|||
|
Enablers 1.
Demonstrate expert awareness of core
cybersecurity theory that encompass standards related to NICE 2.
Gain access to quality information
for decision-making 3.
Gain employment in a cybersecurity
decision-making position 4.
Produce a portfolio of work
as evidence of learning and proficiency |
|||
|
ESSENTIAL
BELIEFS AND AWARENESS Learners
will believe… ·
They are cybersecurity professionals ·
They are needed to protect valued assets ·
They are worth the time, effort and
compensation ·
They are part of an elite group of
professionals Learners
will understand… ·
The global cybersecurity landscapes ·
Pain points of those will valued assets ·
The pros and cons of cyberspace ·
Their function in the system ·
The knowledge and skills (technical and soft)
they need to make a significant impact on keeping the landscape safe |
ESSENTIAL
QUESTION (S) Together
we will consider… As a civilian… What was your
role in the system? What were
your decision-making functions in the system? What were
your valued information assets? What does
security feel like? What happens
in uncertainty? As a Cyber Professional… What is your
role in the system? What is your
decision-making function in the system? What are your
valued information assets? What does
security feel like? What is the
role of the NICE framework in the system? Who needs
your advanced/expert awareness? |
||
|
Learners Proof-of-Work Learners
will demonstrate that they have advanced or expert awareness of… The NICE
principles The state of
cybersecurity in the federal government The “pain
points” of potential clients/customers Their
function in the workplace And
can do…with this mindset Maintain
contextual awareness of what’s going on Practice
empathy with clients/customers Seek out
information from varied perspectives Trust your
team Be decisive |
|||
Stage 2—Assessment Evidence
|
Assessment Measure (s) Tasks
to produce the evidence needed to determine learners’ beliefs and knowledge: ·
Knowledge tests ·
Decision assessment (https://www.ncbi.nlm.nih.gov/pmc/articles/PMC3817076/) ·
Lego Serious Play ·
Visual thinking (graphs) ·
Debate (verbal and written) ·
Social Media posts ·
Question Formulation Technique (QFT) ·
Decision Framework ·
Personal presentation by actual customers
(e.g., risk managers, employees) ·
Videos ·
Case Studies |
Evidence Provided
by the learner in response to learning opportunities and challenges. Measures
will illicit this evidence. ·
90% of learners will pass knowledge tests ·
100% of learners will represent ideas with
Legos (Lego Serious Play) ·
100% of learners will graphically represent
their growing/declining awareness of NICE principles ·
60% of learners will express their thoughts
about decision-making as it relates to the topics (verbally and in writing) ·
100% of learners will complete a decision
framework ·
50% of learners will share their work ideas
with their network (work and non-work) ·
100% of learners will formulate new questions
about the content and way forward ·
Case study analysis (Rubric) |
Stage 3
|
What
concepts, terms and relationships will they understand and remember? NICE
framework
What concepts
and tools with they use/practice? NICE
framework The decision
about how to apply it support business/mission
decisions prioritize
cybersecurity activities, enabling organizations to make informed decisions
about cybersecurity expenditures Framework
uses risk management processes to enable organizations to inform and
prioritize decisions regarding cybersecurity enabling risk
management decisions, Cellular
devices/laptops decision
making about how to manage cybersecurity risk, as well as which dimensions of
the organization are higher priority and could receive additional resources What
concepts/subjects will they relate
to other concepts/subjects? The
relationship between cybersecurity risk and organizational objectives is
clearly understood and considered when making decisions What personal and social implications come
with the new awareness? Where will
the find instrumental value? How will they
know how to keep learning? |
Significant Learning Taxonomy
1.
Demonstrate expert awareness of core
cybersecurity theory that encompass standards related to NICE
2.
Gain access to
quality information for decision-making
3.
Gain employment in a cybersecurity
decision-making position
4.
Produce a portfolio of work as evidence of
learning and proficiency
M More courses I'm working on...
Also, if you create cybersecurity training, want better business outcomes, and better performance at work, come see me on my Everyone Deserves an Ypifany (pronounced "epiphany") Youtube Channel
Want Coaching?
If you would like phone coaching and other coaching opportunities with me, schedule time here


Comments
Post a Comment